MISP - Open Source Threat Intelligence Platform

MISP - Open Source Threat Intelligence and Sharing Platform (formerly known as Malware Information Sharing Platform) is developed as free software/open source by a group of developers from CIRCL and many other contributors.
CIRCL operates several MISP instances (for different types of constituents) in order to improve automated detection and responsiveness to targeted and cybersecurity attacks in Luxembourg and outside. MISP is a platform for sharing threat indicators, threat intelligence within private and public sectors.
Private organisations, organisations, private researchers or CERTs can request access to their respective MISP community.
What is MISP?
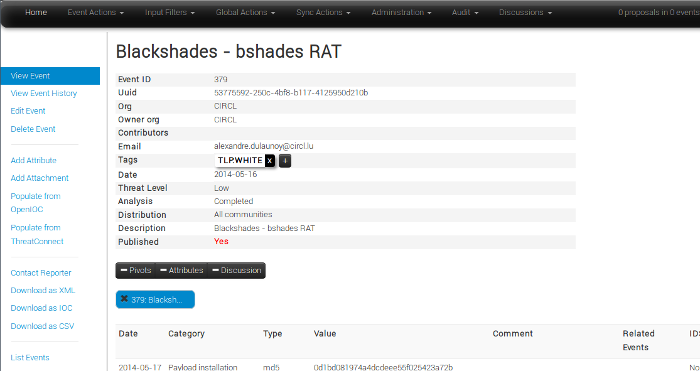
A platform for sharing, storing and correlating Indicators of Compromises of targeted attacks but also threat intelligence such as threat actor information, financial fraud information and many more.
MISP - Open Source Threat Intelligence and Sharing Platform allows organizations to share information such as threat intelligence, indicators, threat actor information or any kind of threat which can structured in MISP. MISP users benefit from the collaborative knowledge about existing malware or threats. The aim of this trusted platform is to help improving the counter-measures used against targeted attacks and set-up preventive actions and detection.
CIRCL MISP information sharing communities - a trusted platform with multiple goals
The objective of the CIRCL MISP - Open Source Threat Intelligence and Sharing Platform is to:
- Facilitate the storage of technical and non-technical information about seen malware and attacks
- Create automatically relations between malware and their attributes
- Store data in a structured format (allowing automated use of the database to feed detection systems or forensic tools)
- Generate rules for Network Intrusion Detection System (NIDS) that can be imported on IDS systems (e.g. IP addresses, domain names, hashes of malicious files, pattern in memory)
- Share malware and threat attributes with other parties and trust-groups
- Improve malware detection and reversing to promote information exchange among organizations (e.g. avoiding duplicate works)
- Create a platform of trust - trusted information from trusted partners
- Store locally all information from other instances (ensuring confidentiality on queries)
For more information: Information Sharing and Cyber Security - The Benefits of the Malware Information Sharing Platform (MISP).
How does MISP work?
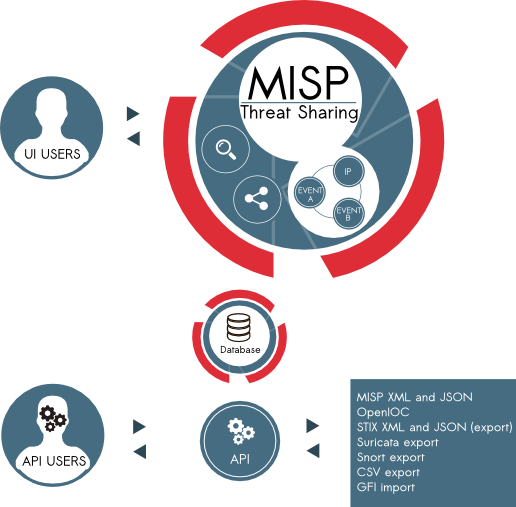
Malware Information Sharing Platform is accessible from different interfaces like a web interface (for analysts or incident handlers) or via a ReST API (for systems pushing and pulling IOCs). The inherent goal of MISP is to be a robust platform that ensures a smooth operation from revealing, maturing and exploiting the threat information.
How to request access?
If you work for private organisations, organisations, CERTs, if you are a trusted security vendor or researcher, you can request access by contacting us. The registration and access requires the use of at least one PGP key per organization.
What are the rules?
The access is free-of-charge. The objective is to stimulate sharing practises among public and private actors. The access is mainly bound to distribution as described in the traffic light protocol.
How the information is shared among the MISP instances worldwide?
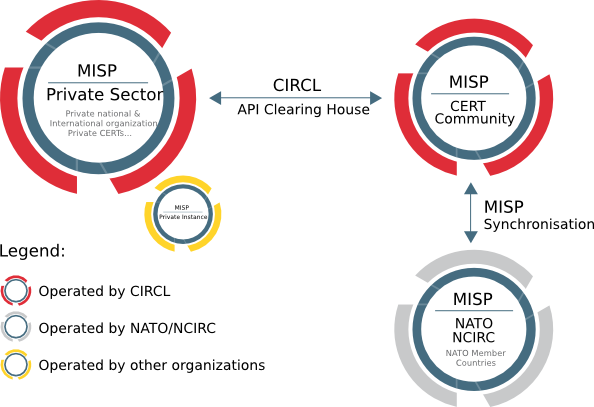
In MISP, there are 4 options regarding distributing events and their respective attributes:
- Your organisation only
- This community only
- Connected communities
- All communities
There is also a set of sharing groups accessible to various members per sector (such as Financial sector).
In the diagram above, you can see an overview of the MISP instances operated by CIRCL. As the distribution is inherent to the connectivity among the MISP instances, participants should keep in mind the overall connectivity to select the appropriate distribution category.
How can I access the MISP API?
When you connect to the MISP platform, there is a specific menu dedicated to automation and export. CIRCL developed a Python library to access MISP API called PyMISP. The API can be used to feed internal security devices (e.g. IDS, SIEM or alike) in order to improve detection. The PyMISP python library documentation is available.
Do I need to install MISP?
No. When you have access to a CIRCL MISP instance, you have an intuitive web interface to find and add threats and indicators. You can directly use the application without the need to install your own MISP instance. The API can be also used with a variety of other security devices if you need to integrate the threats and indicators in your infrastructure (SIEMs, IDS, A/V console, …).
Nevertheless having your own MISP instance has multiple benefits. If you have the capabilities to do so, we strongly recommend a local installation of a MISP instance while syncing with your partners such as CIRCL MISP sharing communities.
I had access to a CIRCL MISP platform but I lost my credentials
If you are part of an organization in MISP, you can ask your MISP organizational admin to reset your password. If not, you can contact CIRCL to reset the credentials.
I found a bug in MISP, what should I do?
If you have found a bug in MISP, we advise you to open an issue on the MISP GitHub issue page. If this is a security vulnerability that cannot be disclosed publicly, contact CIRCL.
Is there a MISP user guide?
A MISP user guide can be found online. The MISP user guide is also available in PDF format, epub format or Kindle mobi format.
Is there any MISP training?
We regularly organize MISP trainings and the MISP training materials are publicly available.


