Last modified: Wed Oct 02 2024 16:09:21 GMT+0200 (Central European Summer Time)
- Taxonomies
- Contributing to Taxonomy
- Reserved Taxonomy
- Adding Taxonomy in MISP
- Adding a private taxonomy
- How to use Taxonomy in MISP
- More options to configure taxonomies.
- Future functionalities related to MISP taxonomies
Taxonomies
In MISP 2.4.X, a flexible mechanism has been introduced to support various taxonomy of classification.
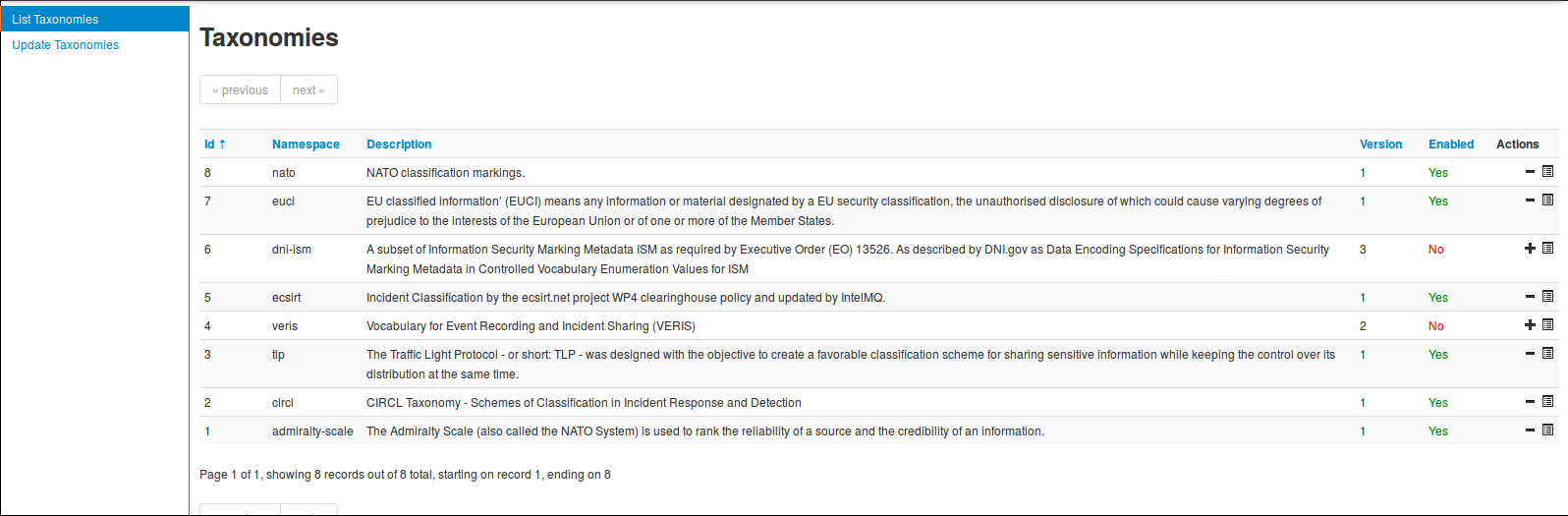
You can access the taxonomy by going into 'Event Actions' and select 'List Taxonomies'. For fresh install, make sure to click 'Update Taxonomies' to view available taxonomies.
A complete list of the available taxonomies PDF are available on the MISP project website.
The following taxonomies can be used in MISP (as local or distributed tags) or in other tools willing to share common taxonomies among security information sharing tools.
Admiralty Scale: The Admiralty Scale (also called the NATO System) is used to rank the reliability of a source and the credibility of an information.
adversary An overview and description of the adversary infrastructure.
CIRCL Taxonomy - Schemes of Classification in Incident Response and Detection CIRCL Taxonomy is a simple scheme for incident classification and area topic where the incident took place.
Cyber Kill Chain from Lockheed Martin as described in Intelligence-Driven Computer Network Defense Informed by Analysis of Adversary Campaigns and Intrusion Kill Chains.
DE German (DE) Government classification markings (VS) Taxonomy for the handling of protectively marked information in MISP with German (DE) Government classification markings (VS).
DHS CIIP Sectors DHS critical sectors as described in https://www.dhs.gov/critical-infrastructure-sectors.
Diamond Model for Intrusion Analysis, a phase-based model developed by Lockheed Martin, aims to help categorise and identify the stage of an attack.
Domain Name Abuse - taxonomy to tag domain names used for cybercrime. Use europol-incident to tag abuse-activity
eCSIRT eCSIRT incident classification Appendix C of the eCSIRT EU project including IntelMQ updates.
ENISA ENISA Threat Taxonomy - A tool for structuring threat information as published
Estimative Language Estimative language - including likelihood or probability of event based on the Intelligence Community Directive 203 (ICD 203) (6.2.(a)).
[EU Marketop and Publicadmin]EU critical sectors Market operators and public administrations that must comply to some notifications requirements under EU NIS directive.
EUCI EU classified information (EUCI) means any information or material designated by a EU security classification, the unauthorised disclosure of which could cause varying degrees of prejudice to the interests of the European Union or of one or more of the Member States as described.
Europol Incident EUROPOL class of incident taxonomy
Europol Events - EUROPOL type of events taxonomy
FIRST CSIRT Case FIRST CSIRT Case Classification.
FIRST Information Exchange Policy (IEP) framework
Information Security Indicators Information security indicators have been standardized by the ETSI Industrial Specification Group (ISG) ISI. These indicators provide the basis to switch from a qualitative to a quantitative culture in IT Security Scope of measurements: External and internal threats (attempt and success), user's deviant behaviours, nonconformities and/or vulnerabilities (software, configuration, behavioural, general security framework).
Information Security Marking Metadata (ISM) V13 as described by DNI.gov.
Malware classification based on different categories. Based on a SANS whitepaper about malware.
Malware Type and Platform classification based on Microsoft's implementation of the Computer Antivirus Research Organization (CARO) Naming Scheme and Malware Terminology. Based on Microsoft Malware naming conventions, Microsoft Glossary, Microsoft Objective Criteria, and CARO's definitions. Malware families are extracted from Microsoft SIRs since 2008 based on Microsoft Malware, virus, and threat encyclopedia. Note that SIRs do NOT include all Microsoft malware families.
MISP taxonomy to infer with MISP behavior or operation.
ms-caro-malware Malware Type and Platform classification based on Microsoft's implementation of the Computer Antivirus Research Organization (CARO) Naming Scheme and Malware Terminology.
NATO Classification Marking Marking of Classified and Unclassified materials as described by the North Atlantic Treaty Organization, NATO.
Open Threat Taxonomy v1.1 (SANS) based on James Tarala of SANS (http://www.auditscripts.com/resources/open_threat_taxonomy_v1.1a.pdf).
The Permissible Actions Protocol - or short: PAP PAP was designed to indicate how the received information can be used. It's a protocol/taxonomy similar to TLP informing the recipients of information what they can do with the received information.
Status of events used in Request Tracker.
Classification based on malware stealth techniques. Described in Introducing Stealth Malware Taxonomy
TLP - Traffic Light Protocol The Traffic Light Protocol - or short: TLP - was designed with the objective to create a favorable classification scheme for sharing sensitive information while keeping the control over its distribution at the same time.
Vocabulary for Event Recording and Incident Sharing VERIS
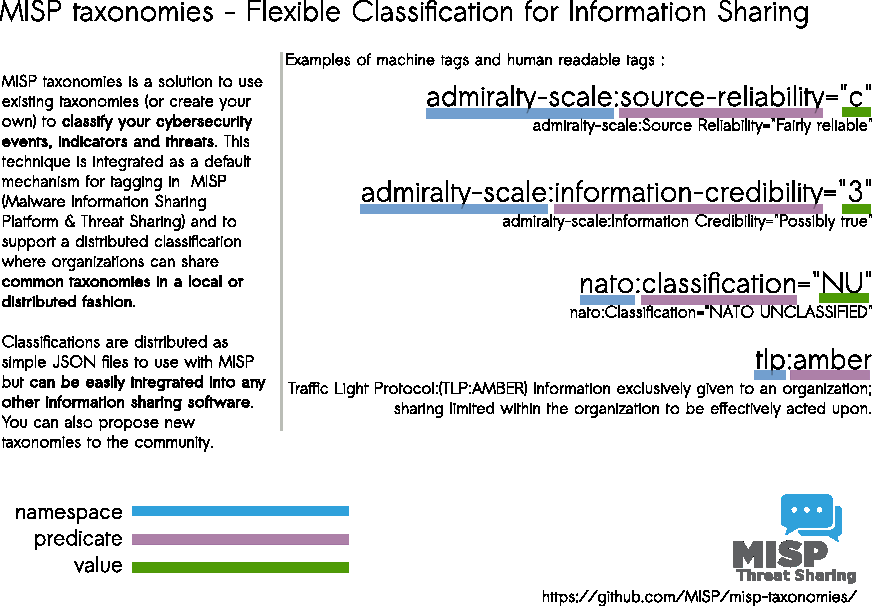
A taxonomy contains a series of tags that can be used as normal tags in your MISP instance.
Tagging is a simple way to attach a classification to an event. In the early version of MISP, tagging was local to an instance. Classification must be globally used to be efficient. After evaluating different solutions of classification, we build a new scheme using the concept of machine tags.
Taxonomy is a classification of informations. Taxonomies are implemented in a simple JSON format. Anyone can create their own taxonomy or reuse an existing one.
Taxonomies are in an independent git repository.
These can be freely reused and integrated in other threat intel tools.
The advantage is that you can set a specific tag as being exportable. This means that you can export your classification with other MISP instance and share the same taxonomies. Tagging is a simple way to attach a classification to an event.
Classification must be globally used to be efficient.
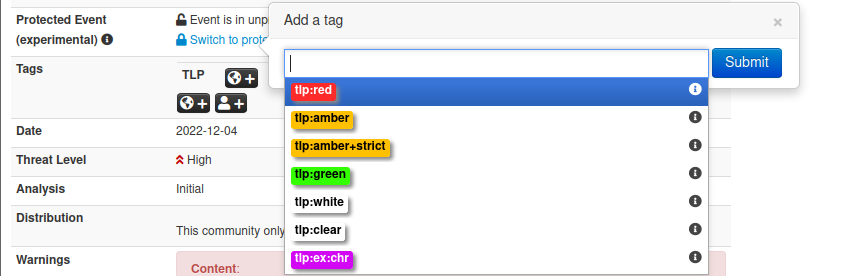
If you want to enable a specific taxonomy, you can click on the cross to enable it.
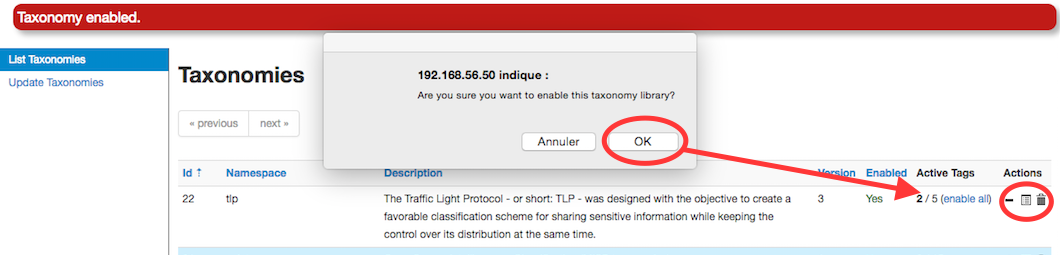
Then you can even cherry-pick the tags you want to use on the system. If you want to use the whole taxonomy, select all and then click on the cross in the top left.
Contributing to Taxonomy
It is quite easy. Create a JSON file describing your taxonomy as triple tags.
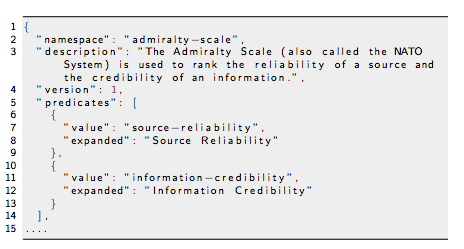
(e.g. check an existing one like Admiralty Scale), create a directory matching your name space, put your machinetag file in the directory and pull your request. Publishing your taxonomy is as easy as a simple git pull request on misp-taxonomies (https://github.com/MISP/misp-taxonomies). That's it. Everyone can benefit from your taxonomy and can be automatically enabled in information sharing tools like MISP.
Reserved Taxonomy
The following taxonomy namespaces are reserved and used internally to MISP.
- galaxy mapping taxonomy with cluster:element:"value".
Adding Taxonomy in MISP
How are taxonomies integrated in MISP?
MISP administrators have only to import (or even cherry pick) the namespace or predicates they want to use as tags.
Tags can be exported to other instances.
Tags are also accessible via the MISP REST API.
For more information, "Information Sharing and Taxonomies Practical Classification of Threat Indicators using MISP" presentation given to the last MISP training in Luxembourg.
Adding a private taxonomy
$ cd /var/www/MISP/app/files/taxonomies/
$ mkdir privatetaxonomy
$ cd privatetaxonomy
$ vi machinetag.json
Create a JSON file describing your taxonomy as triple tags.
For example :
mkdir sample
cd sample
vim machinetag.json
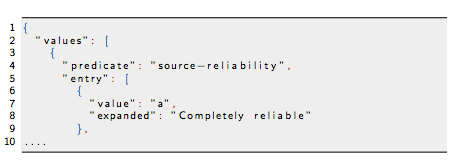
Sample JSON with triple tags. You can use the JSON validator to be sure that there is no syntax error.
{
"namespace": "sample",
"description": "Some descriptive words",
"version": 1,
"predicates": [
{
"value": "my-predicate",
"expanded": "my-predicate"
}
],
"values": [
{
"predicate": "my-predicate",
"entry": [
{
"value": "a-value",
"expanded": "A value"
}
]
}
]
}
Go to MISP Web GUI taxonomies/index and update the taxonomies once you are happy with your file. The newly created taxonomy should be visible. Now you need to activate the tags within your taxonomy.
How to use Taxonomy in MISP
Filtering the distribution of events among MISP instances
Applying rules for distribution based on tags:
MISP Taxonomies - tools
- machinetag.py is a parsing tool to dump taxonomies expressed in Machine Tags (Triple Tags) and list all valid tags from a specific taxonomy.
% cd tools
% python machinetag.py
admiralty-scale:source-reliability="a"
admiralty-scale:source-reliability="b"
admiralty-scale:source-reliability="c"
admiralty-scale:source-reliability="d"
admiralty-scale:source-reliability="e"
admiralty-scale:source-reliability="f"
admiralty-scale:information-credibility="1"
admiralty-scale:information-credibility="2"
admiralty-scale:information-credibility="3"
admiralty-scale:information-credibility="4"
admiralty-scale:information-credibility="5"
admiralty-scale:information-credibility="6"
...
- PyTaxonomies - Python module to use the MISP Taxonomies
Other use cases using MISP taxonomies
Tags can be used to:
Set events for further processing by external tools (e.g. VirusTotal auto-expansion using Viper).
Ensure a classification manager classes the events before release (e.g. release of information from air-gapped/classified networks).
Enrich IDS export with tags to fit your NIDS deployment.
More options to configure taxonomies.
For MISP users and organisations, it's important to show the important contextualised information and especially the taxonomies which are important to your use-case. Once a taxonomy is enabled and available for use in MISP, there are two more options a admin can be set to encourage the use of particular taxonomies. Both are found in Event Actions > List Taxonomies menu.
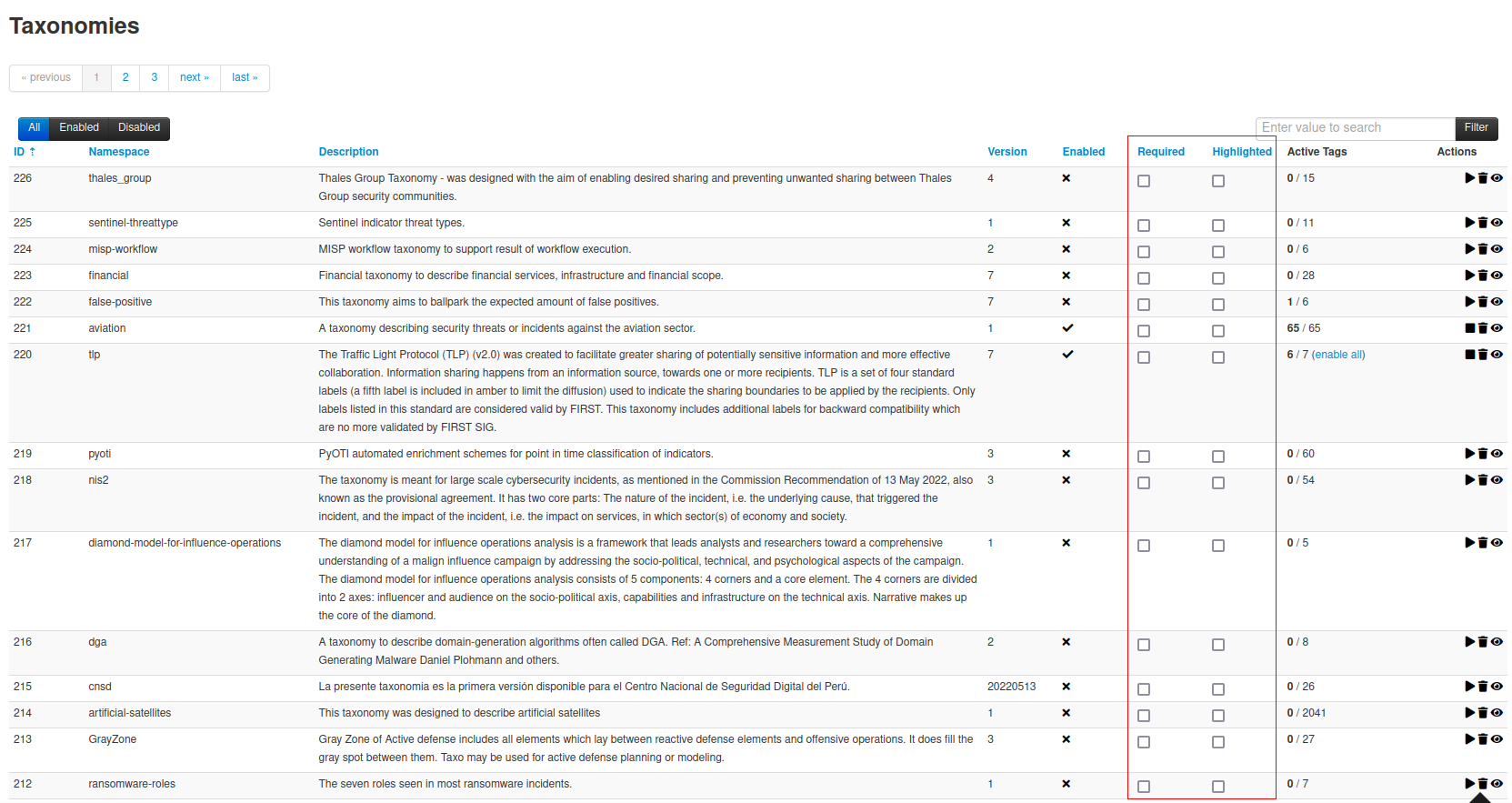
Setting a taxonomy as "Highlighted"
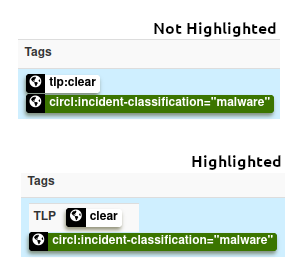
If a taxonomy is highlighted, its namespace will appear in a visible box, even if it is not set in the event.
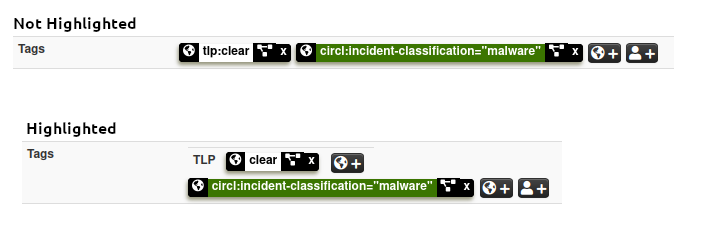
Tags are also hilighted in the event list.
It is also easier to add an highlighted tag to an event.
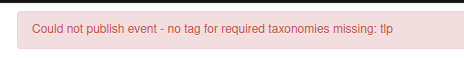
Setting a taxonomy as "Required"
If taxonomies are set as required, a message will be visible on the tag list of the event, enumerating the missing required taxonomies still missing.
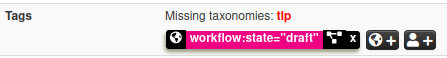
An event will not be published if it is not tagged with at least one of tag of each required taxonomy.
Future functionalities related to MISP taxonomies
Sighting support (thanks to NCSC-NL) is integrated in MISP allowing to auto expire IOC based on user detection.
Adjusting taxonomies (adding/removing tags) based on their score or visibility via sighting.
Simple taxonomy editors to help non-technical users to create their taxonomies.
Filtering mechanisms in MISP to rename or replace taxonomies/tags at pull and push synchronisation.
More public taxonomies to be included